DeFi Hack Postmortem: How Reactive Contracts Could Have Protected Loan Positions During the rsETH Exploit
In DeFi Hack Postmortem Part 1, we looked at how Reactive Contracts address the root cause of bridge exploits: the gap between what a validator claims has happened and what actually has happened on-chain. That's the prevention side: stopping the hack before it starts.
But prevention only works if you control the infrastructure. Most DeFi users don't. They're downstream, holding positions on lending protocols like Aave, using tokens like rsETH as collateral, and trusting that the systems above them will hold.
On April 18th 2026, that trust broke. And for users with rsETH-collateralized positions on Aave, the question wasn't whether the bridge could have been built differently. It was: how do I get out before everything collapses?
This is where Reactive Contracts solve a different problem entirely. Not bridge security but automated, on-chain self-defense.
Aave's Collateral Damage
As covered in Part 1, the Kelp bridge exploit drained 116,500 rsETH in a single block. But the real story for Aave users wasn't the exploit itself. It was what happened next.
Aave froze rsETH markets within hours. That freeze didn't just contain the attacker's positions. It locked in every legitimate user who had rsETH exposure.
What followed was a liquidity cascade. Whales and large funds pulled billions from Aave's pools. WETH reserves hit 100% utilization across Ethereum, Arbitrum, Base, Linea, and Mantle, with idle balances below $20 on every chain. The remaining depositors couldn't withdraw. Some borrowed roughly $300M against their own trapped stablecoin deposits at steep losses, just to access liquidity.
For ordinary users with rsETH positions on Aave, the window to act was measured in minutes. If you weren't watching the chain at the exact moment the exploit happened, you were already too late.
Speed Gap
DeFi lending works on health factors. Your health factor is the ratio between the value of your collateral and what you've borrowed. Drop below 1.0 and you're liquidatable. Most users try to maintain a buffer, keeping their health factor at 1.5 or 2.0 to absorb normal price swings.
But bridge exploits aren't normal price swings. When the Kelp bridge was drained, the situation didn't unfold over hours or days. The adapter balance went from 116,723 rsETH to 223 rsETH in a single block. The attacker's positions on Aave settled with health factors between 1.01 and 1.03, razor-thin margins that any small price movement would trigger.
For legitimate users, the timeline was brutal. The exploit happened. News spread. Panic set in. Whales moved first, draining liquidity pools before smaller users could react. By the time most people understood what was happening, WETH utilization was at 100% and withdrawals were frozen.
This is the core failure mode that Reactive Contracts address on the user side: the assumption that human attention and reaction time are sufficient to manage DeFi risk.
They aren't. Markets move faster than people. Exploits move faster than markets.
Reactive Defense
For Aave position protection, a Reactive contract works like this:
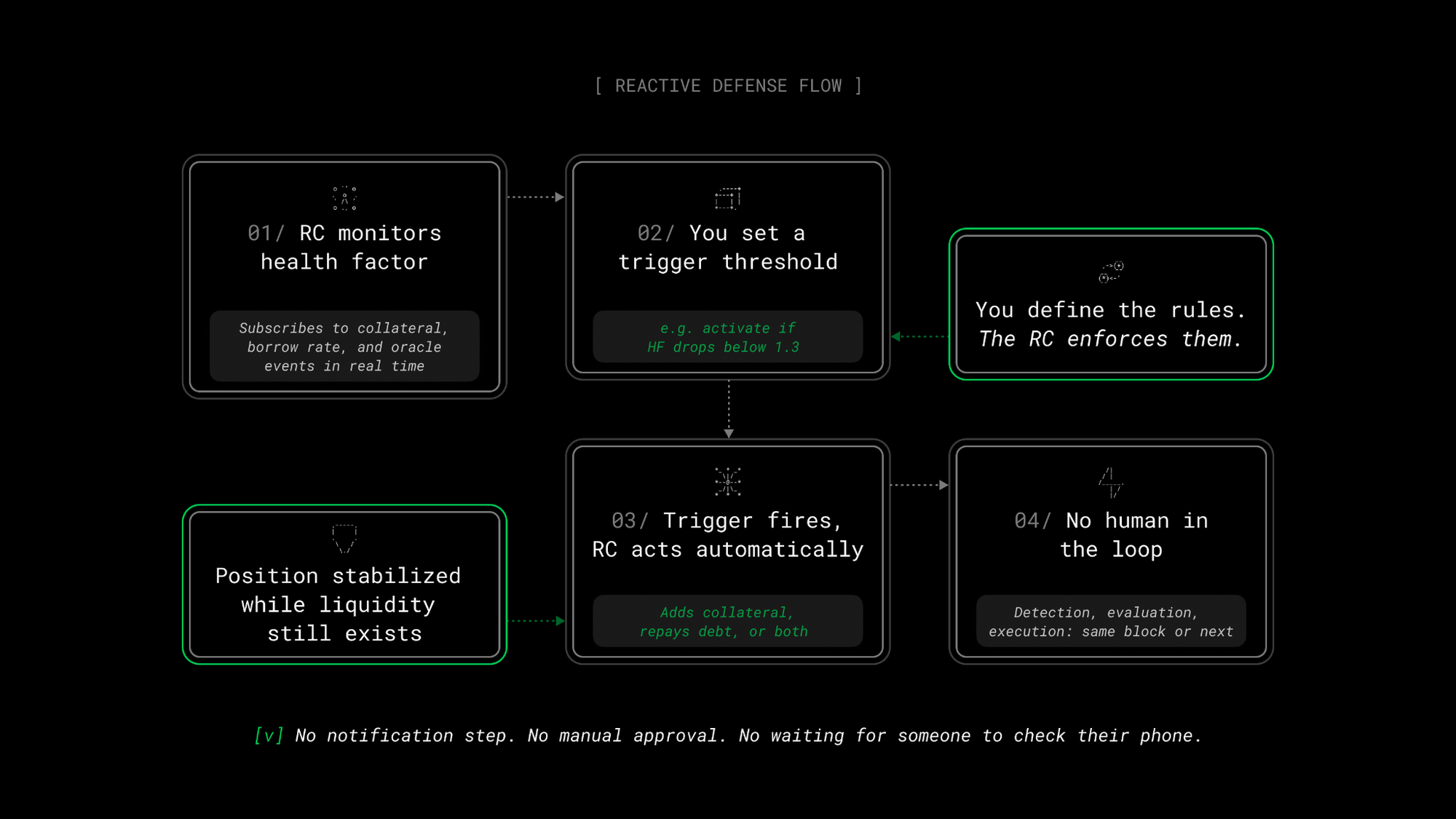
It's the difference between a smoke alarm that activates the sprinkler system and one that just beeps.
Consider a user who held rsETH as collateral on Aave with a health factor of 1.5 before the exploit.
Without a Reactive Contract: The exploit drains the bridge. rsETH begins to depeg. The user's health factor drops. By the time they notice (if they notice at all) WETH pools are at 100% utilization. They can't withdraw, can't repay easily, and can't add collateral from external sources because the markets are frozen. They're trapped, watching their position deteriorate with no way to act.
With a Reactive Contract: The RC detects the health factor dropping toward the trigger threshold. Before WETH pools are fully drained, before markets are frozen, the RC executes the protective action: repaying debt, adding collateral, or both. The position is stabilized or unwound while liquidity still exists. The user doesn't need to be online, doesn't need to be watching, doesn't need to compete with whales for exit liquidity.
Timing is key. In the Kelp aftermath, the first movers (whales and large funds) pulled out billions before most users could react. Reactive Contracts level that playing field. An automated on-chain response doesn't sleep, doesn't panic, and doesn't wait in line. It executes at the speed of the chain.
Why Bots Fall Short
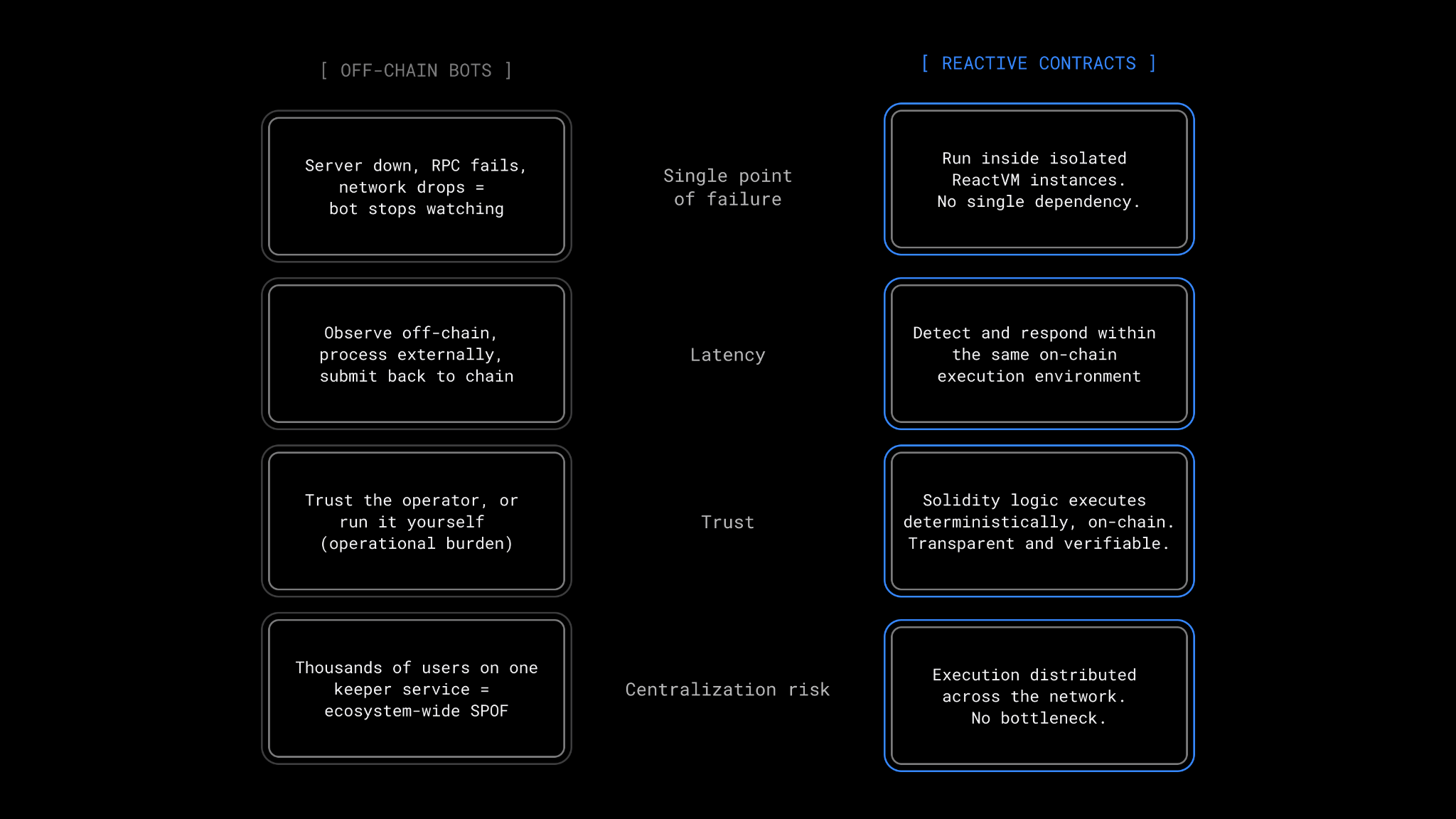
The obvious counter-argument: why not just use an off-chain bot to monitor your position and act when needed? Off-chain bots are better than nothing. But they have structural weaknesses that Reactive Contracts don't share.
Bigger Picture
The Kelp exploit exposed something the DeFi ecosystem has been slow to acknowledge: composability is also a liability.
When everything works, composability is DeFi's superpower. Tokens flow between protocols. Yield stacks on yield. Collateral moves across chains. But when one layer fails, the damage propagates through every protocol that touches it. A bridge exploit becomes a lending crisis becomes a liquidity crisis becomes a confidence crisis.
Reactive Contracts don't fix composability risk at the protocol level. That requires the kind of architectural changes discussed in Part 1. What they do is give individual users the ability to defend their own positions, automatically, at the speed of the chain, without depending on protocol governance to act fast enough, or whale liquidity to still be available, or their own attention to be perfectly timed.
In a system where a single forged message can cascade through the entire DeFi lending stack in hours, that kind of automated self-defense is must-have infrastructure.
About Reactive Network
Reactive Network is an EVM automation layer built around Reactive Contracts — event-driven smart contracts for cross-chain, on-chain automation.
Reactive Contracts monitor event logs across EVM chains and execute Solidity logic when subscribed events occur, autonomously deciding when to send cross-chain callback transactions. This model supports conditional cross-chain state changes and continuous cross-chain workflows.
Website | Blog | X | Telegram | Discord | Docs
Build once — react everywhere!