DeFi Hack Postmortem: Why Reactive Contracts Are the Bridge Security Model DeFi Needs

On April 18th, 2026, someone sent a fake message to a cross-chain bridge and walked away with $293 million.
The target was Kelp DAO, a liquid restaking protocol on Ethereum. The bridge connecting it to other blockchains was configured with a single validator, one computer responsible for confirming whether incoming cross-chain messages were real. The attacker forged a message claiming tokens had arrived from another chain. The bridge believed it and released 116,500 rsETH, roughly 18% of the token's supply.
No encryption was broken. No smart contract bug was exploited. The system worked exactly as designed. It just wasn't designed to handle a lie.
DeFi's Recurring Disaster
Cross-chain bridges let users move tokens between blockchains. The basic flow is a bridge that locks tokens on one chain, sends a message to the other chain confirming the lock, and releases equivalent tokens on the other side.
The entire model depends on that middle step, the message being truthful. Most bridges delegate message verification to a set of validators or signers. If enough of them are compromised, tricked, or (as with Kelp) if there simply aren't enough of them, the bridge will release tokens against fabricated claims.
This isn't a new problem. Ronin lost $625M this way. Wormhole lost $320M. Nomad lost $190M. The pattern repeats because the underlying architecture hasn't changed: bridges still rely on small groups of external parties to attest that something happened on another chain, and attestation can be forged.
Root Cause
Every major bridge exploit shares the same structural flaw. The destination chain doesn't independently verify what has happened on the origin chain. Instead, it trusts a relayed message: a claim made by a third party that an event occurred.
The flow looks like this:
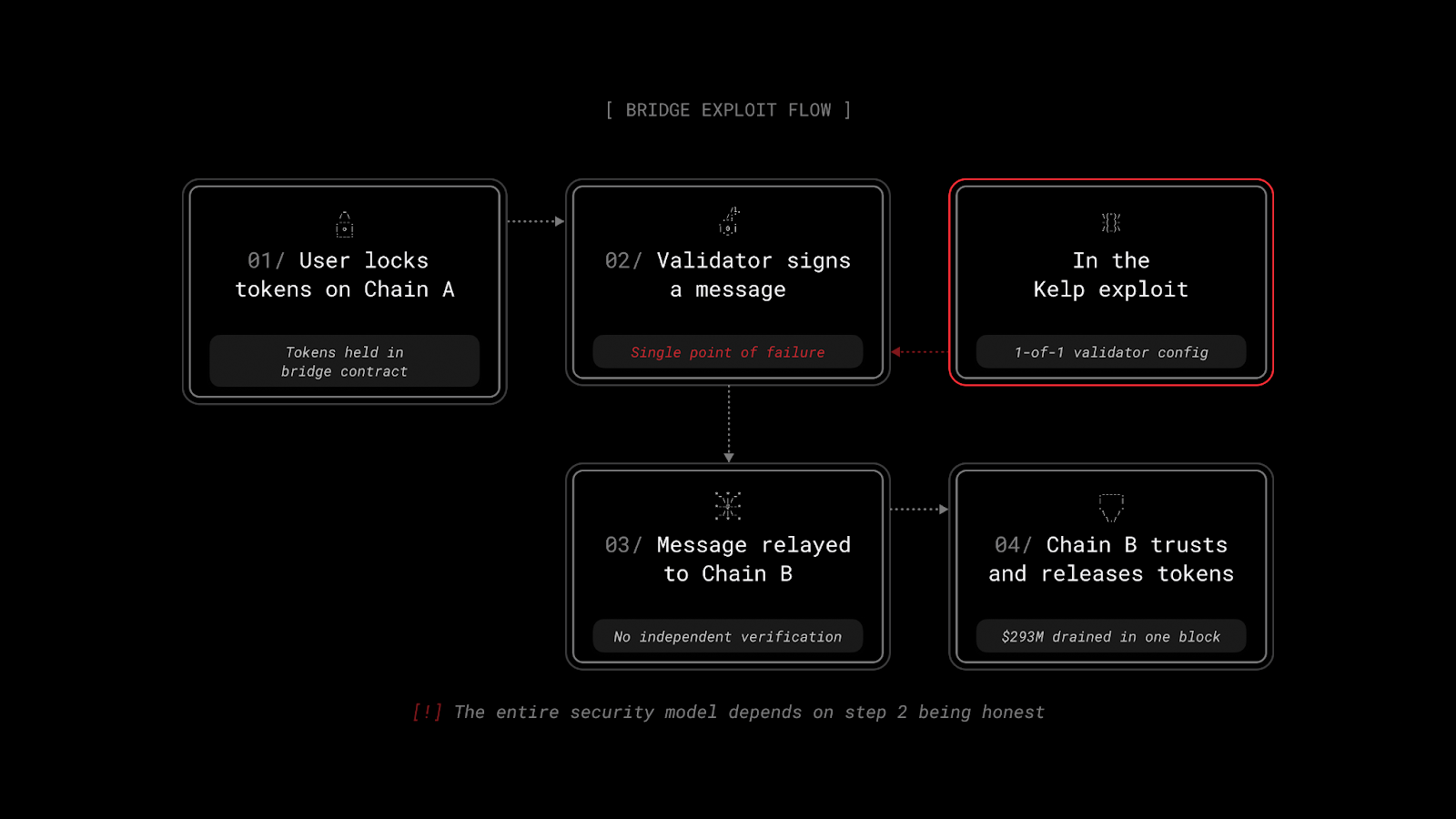
The security of the entire system sits in step 2. Compromise the validator (or, in Kelp's case, simply have only one), and the bridge can’t tell the difference between a real transfer and a fabricated one.
This is what makes bridge exploits so much larger than typical DeFi hacks. The bridge isn't checking whether tokens have actually been locked. It's checking whether a trusted party says they have.
Reactive Model
Reactive Contracts, built on Reactive Network, take a structurally different approach to cross-chain communication. Instead of relying on validators to relay messages between chains, they subscribe directly to on-chain event logs and execute logic when specific conditions are met.
Here's what that changes in practice:

In a traditional bridge, you trust validators to accurately report what has happened. With Reactive Contracts, the contract reads directly from the origin chain's own event logs.
Trust lives in the origin chain's own consensus, not in an external validator set. To fake an event, you'd need to compromise the origin chain itself.
Applied to Kelp
In the Kelp exploit, the attacker forged a LayerZero packet that appeared to confirm a token transfer. The single validator approved it, and the bridge released $293M in rsETH from its Ethereum-side adapter in a single block.
Under a Reactive Contract model, there's no packet to forge. The contract would be watching for a specific burn event on the origin chain. If no tokens have actually been burned, there's no event in the log. No event, no release. The attack vector simply doesn't exist.
Beyond eliminating the forged-message problem, Reactive Contracts can enforce additional conditions before releasing tokens: checking that burn amounts on the origin chain match the expected release on the destination, verifying that the originating contract is recognized, enforcing rate limits or volume caps, all within the same execution flow. These aren't bolted-on safety mechanisms. They're part of how the Reactive contract operates.
Architectural Comparison
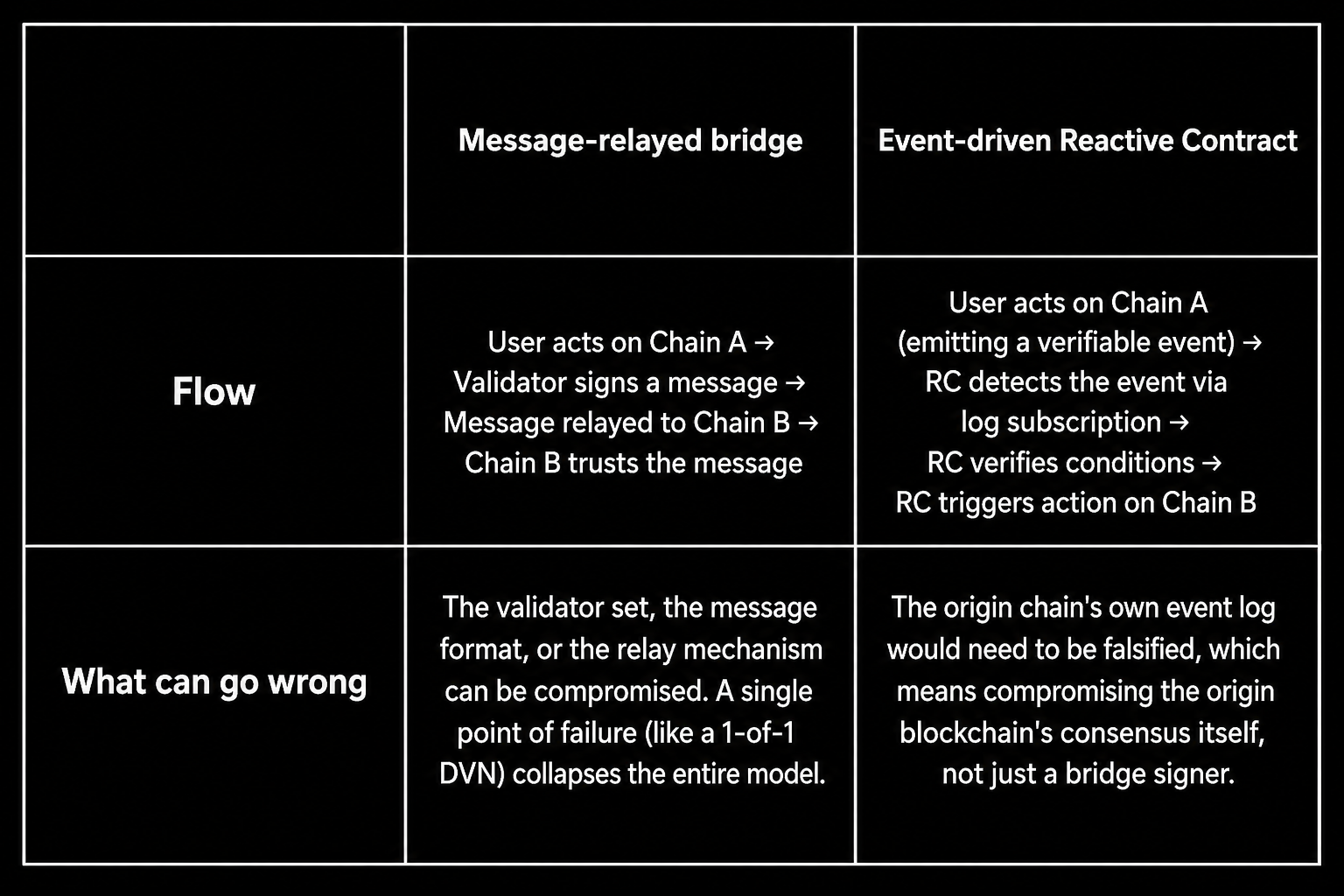
That's a categorically different security boundary. It moves the trust anchor from a small external validator set to the consensus mechanism of the origin chain, which is exactly the security guarantee users believe they are getting when they use a bridge in the first place.
Going Forward
The Kelp incident has already triggered some recovery. Arbitrum's Security Council froze $71M in ETH linked to the attacker. Aave is stress-testing its Umbrella bad-debt backstop for the first time in production. Governance proposals are flying across every affected protocol.
But the pattern won't stop until the architecture changes. As long as bridges rely on attested messages (claims about what has happened on another chain rather than direct verification), they'll remain the highest-value target in DeFi. Every bridge holding significant liquidity is one compromised signer away from the same outcome.
Reactive Contracts don't eliminate all cross-chain risk. But they do eliminate the specific class of vulnerability behind Kelp and every major bridge exploit before it: the gap between what a validator says has happened and what has actually happened on-chain.
Part 2 will cover the other side of this incident: once the damage was done and rsETH began to depeg, how could individual users with Aave positions have protected themselves? We'll walk through how a Reactive Contract monitoring health factors could have automatically unwound positions before the liquidation cascade hit.
About Reactive Network
Reactive Network is an EVM automation layer built around Reactive Contracts — event-driven smart contracts for cross-chain, on-chain automation.
Reactive Contracts monitor event logs across EVM chains and execute Solidity logic when subscribed events occur, autonomously deciding when to send cross-chain callback transactions. This model supports conditional cross-chain state changes and continuous cross-chain workflows.
Website | Blog | X | Telegram | Discord | Docs
Build once — react everywhere!